What this gives the business
What you send when privacy gets challenged
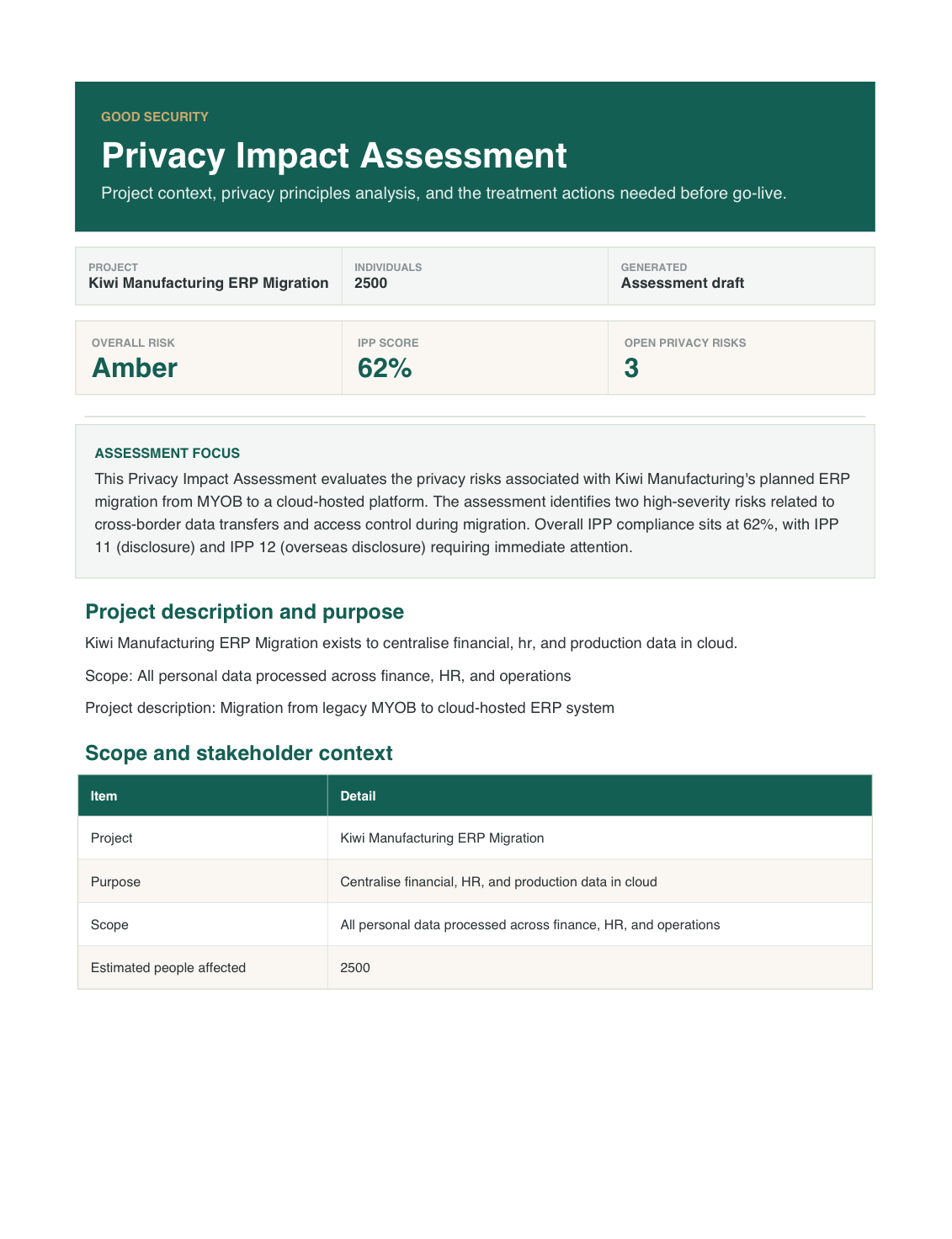
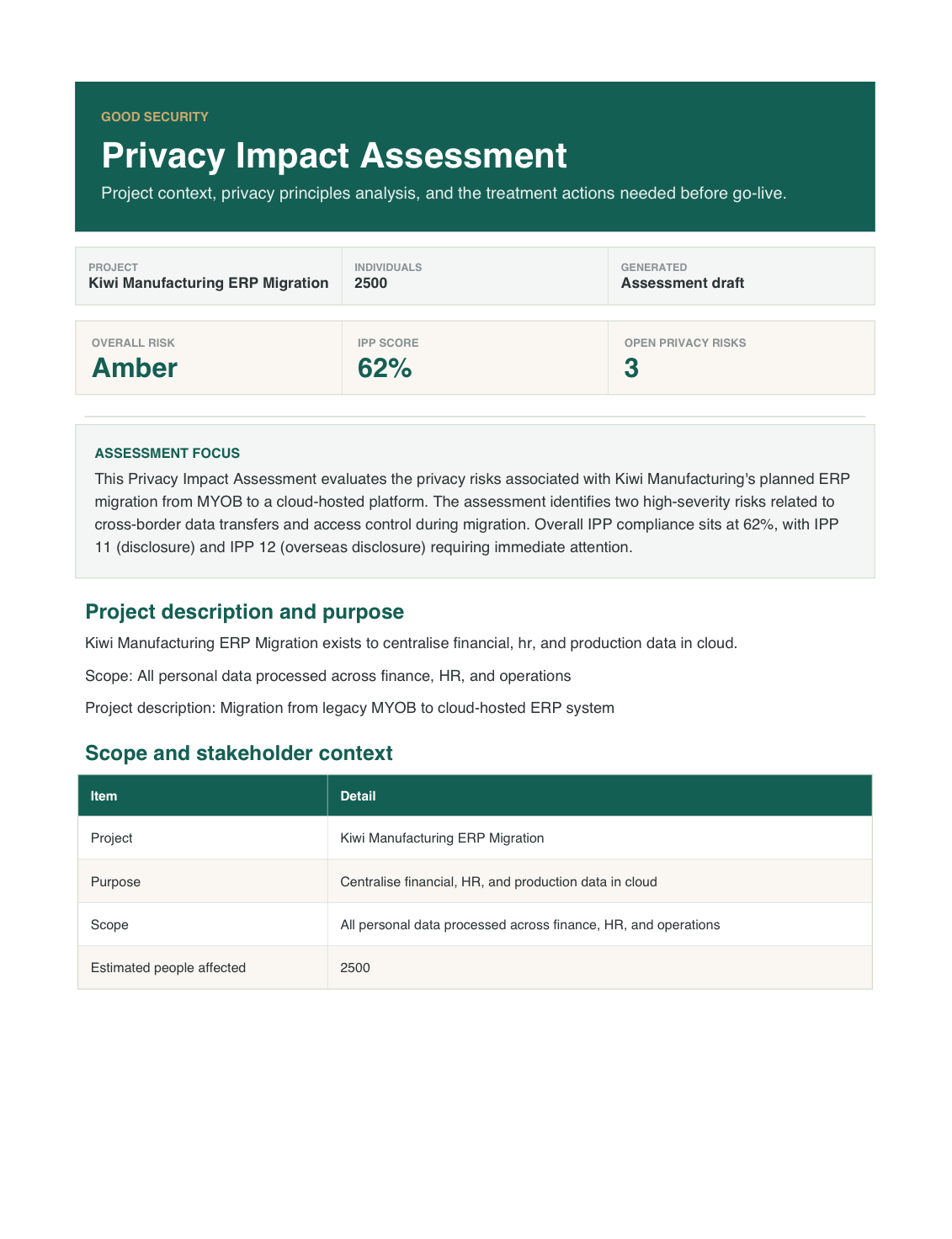
A fictional privacy impact assessment covering project context, information flows, IPP analysis, and treatment actions.
Service
Work out whether a project creates privacy risk before launch, with clear decisions, mitigations, and evidence you can stand behind.
What this gives the business
What you send when privacy gets challenged
A fictional privacy impact assessment covering project context, information flows, IPP analysis, and treatment actions.
The pressure
You get a structured privacy impact assessment that surfaces the material risks, required controls, and decisions before the change hardens.
When a new project changes how personal information is collected, used, or shared, the risk is not just legal. It can slow delivery, create customer trust issues, and force rework after launch. A privacy impact assessment helps you surface those issues early enough to do something useful about them.
Good Security reviews the proposal, tests it against privacy obligations and real operating risk, and leaves you with a written assessment, practical mitigations, and a decision record the project team can work from.
Deliverables
A detailed PIA report, specific risk treatment recommendations per identified risk, privacy-by-design guidance, and a mapping to the relevant Information Privacy Principles
Detailed assessment documenting the project scope, personal information flows, identified privacy risks, impact ratings, and recommended controls.
Specific, practical recommendations for each identified risk, including control options, implementation guidance, and residual risk assessment.
Proactive recommendations for embedding privacy controls into the project design rather than retrofitting them after implementation.
Mapping of project activities to relevant Information Privacy Principles, identifying applicable obligations and demonstrating compliance approach.
What that looks like in practice
The PIA output sets out the project context, the personal information involved, the risk areas, the required mitigations, and the decisions leadership or the project team must make before proceeding.
Outcomes
Project privacy risk shows up before go-live, mitigations land while they can still shape delivery, and you've a defensible decision record
Process
Four steps from defining project and data context, through impact assessment and mitigation agreement, to a pre-launch walkthrough of what must change
We confirm what is changing, which personal information is involved, and where the highest sensitivity sits.
Good Security reviews the design against privacy obligations, practical risk, and customer trust considerations.
The assessment turns into concrete changes, decisions, and owners rather than a generic warning list.
You receive the written assessment and a walkthrough of what must happen before launch or approval.
Related services
Usually pairs with the personal data inventory so the PIA starts from a known map, or privacy breach readiness if the project raises incident exposure
Asset, Data & Access Management
Map where personal information enters your business, where it goes, and who is responsible before privacy obligations or customer questions catch you out.
Risk & Vendor Management
Get the business ready to respond to a privacy breach with a practical plan, decision guide, and rehearsal before the real call comes in.
Book a call and we'll talk through whether this is the right next step, what you'd walk away with, and how it sits alongside anything the business already has in place.
Questions buyers ask before committing
A new project or change to data handling is moving ahead and privacy risk is being discovered too late Use this when a new data use, system, or process needs privacy review before go-live or procurement sign-off.
You get a structured privacy impact assessment that surfaces the material risks, required controls, and decisions before the change hardens.