What this gives the business
Every customer demand, with owners
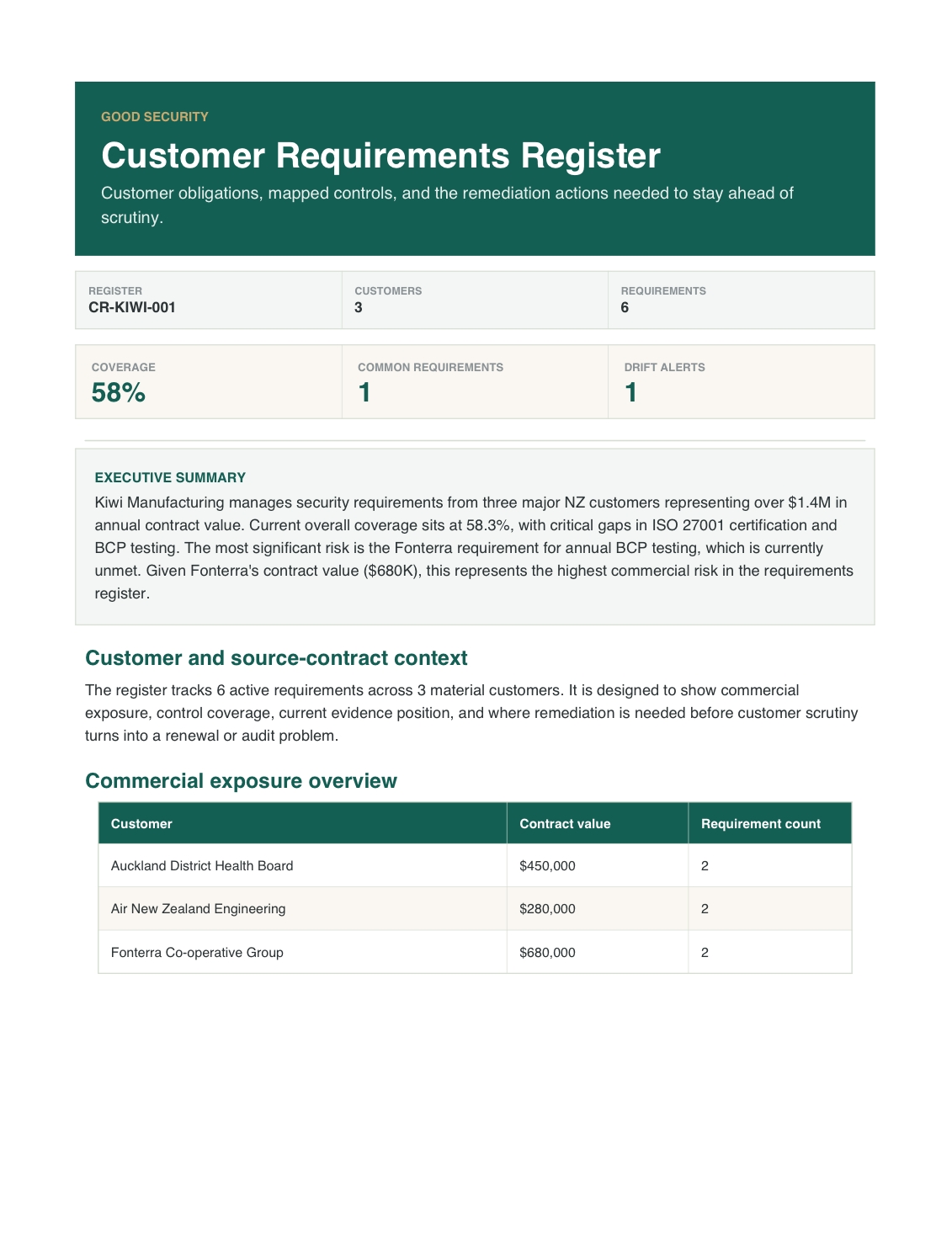
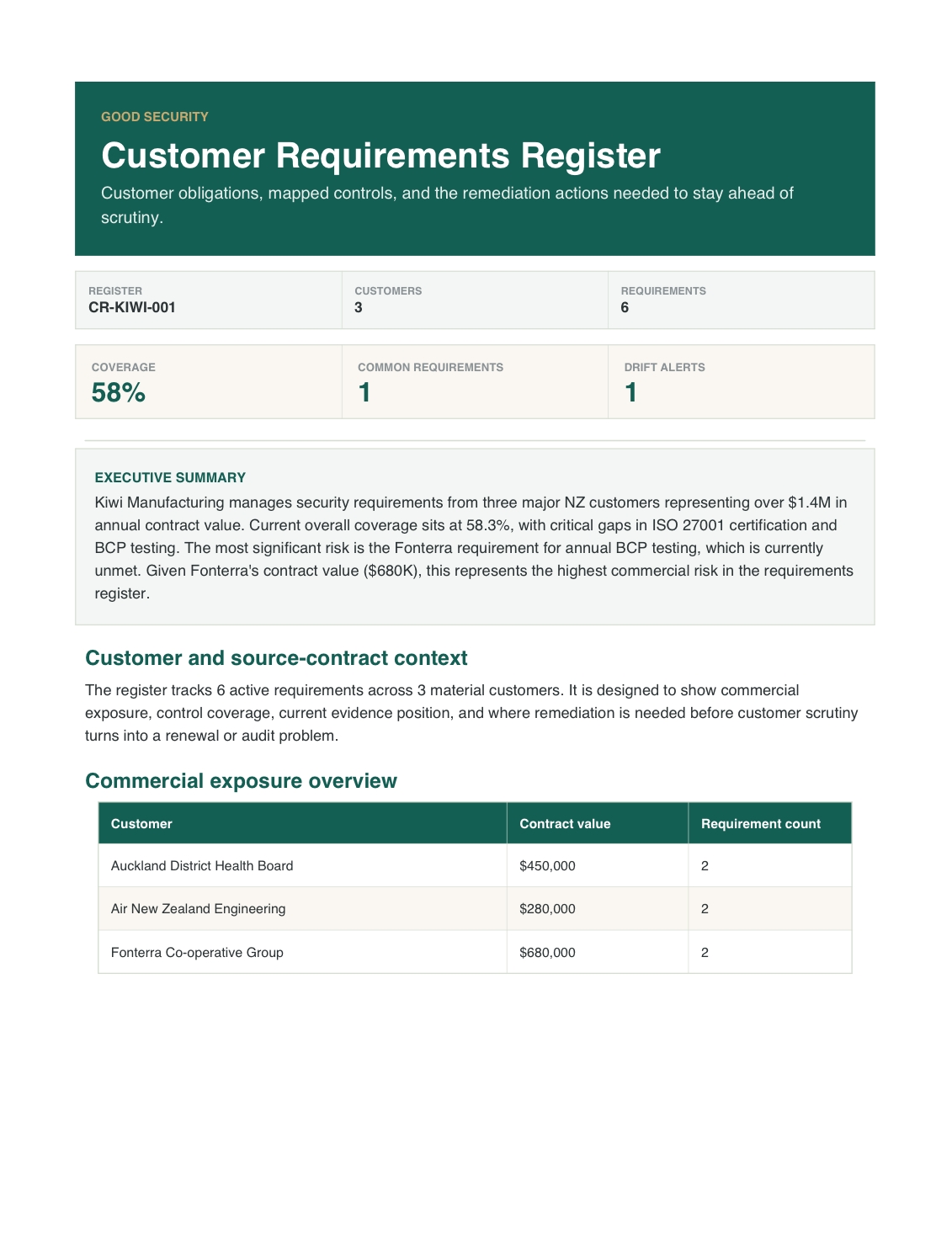
A fictional register showing customer obligations, mapped controls, evidence status, remediation, and review cadence.
Service
Keep customer security and privacy obligations in one register so commitments, exceptions, and evidence do not disappear between contracts.
What this gives the business
Every customer demand, with owners
A fictional register showing customer obligations, mapped controls, evidence status, remediation, and review cadence.
The pressure
The business gets one working requirements register so obligations, owners, and evidence gaps stop living in separate threads.
Customer requirements pile up across contracts, questionnaires, renewal notes, and email promises. Without one working register, you over-commit, misses obligations, or cannot prove what was agreed when scrutiny returns.
Good Security consolidates those requirements, maps them to owners and evidence, and leaves you with a register that shows what is already covered, what still needs work, and where decisions or exceptions sit.
Deliverables
A centralised customer requirements register, a control mapping matrix across buyers, impact assessments for obligation changes, and gap improvement guidance
Centralised register of all customer security requirements mapped to your existing controls, with compliance status and gap identification.
Matrix showing how your security controls satisfy requirements across multiple customers, identifying shared and unique obligations.
Assessment of business and technical impact when customer requirements change or new obligations are introduced.
Practical recommendations for addressing control gaps identified during requirement mapping, prioritised by customer criticality.
What that looks like in practice
The requirements register shows each customer obligation, the source it came from, the current owner, the available evidence, the unresolved gaps, and the next review or remediation action.
Outcomes
Customer obligations sit in one place, ownership for follow-through is clearer, questionnaire and contract responses speed up, and missed commitments stop slipping through
Process
Four steps from collecting the customer commitments, through normalising obligations and mapping them to owners and proof, to handing over a living register
We gather the relevant contract clauses, due-diligence responses, and ongoing customer requirements already in play.
Good Security turns them into a consistent register instead of a mix of one-off wording and scattered notes.
Each requirement is connected to the control, evidence, or decision point you need to manage it.
You receive a register you can use for renewals, reviews, and ongoing obligation tracking.
Related services
Usually pairs with the vendor risk register when customer obligations flow down to suppliers, or the security questionnaire response engine for the live buyer conversation
Risk & Vendor Management
Track supplier security risk in one place so onboarding, renewals, and exceptions stop living in scattered emails and spreadsheets.
Stay compliant
Answer customer and partner security questionnaires without slowing deals down or rebuilding the response every time.
Book a call and we'll talk through whether this is the right next step, what you'd walk away with, and how it sits alongside anything the business already has in place.
Questions buyers ask before committing
Customer security promises are spread across contracts, questionnaires, and renewal notes, and nobody has one trusted register Use this when customer commitments are already accumulating and the business needs one reliable record before promises get missed.
The business gets one working requirements register so obligations, owners, and evidence gaps stop living in separate threads.